If you’ve had a password hacked recently, you aren’t alone.
The volume of password attacks has soared to an estimated 921 attacks every second. That’s a 74% rise in one year, according to the latest Microsoft Digital Defense Report.
Big technology firms including Microsoft would prefer the world of passwords is eradicated, and they’ve been making changes for an online future that is less reliant on the vulnerable security step.
Microsoft users can already securely gain access to Windows, Xbox, and Microsoft 365 without using a password through apps like Microsoft Authenticator, and technologies including fingerprints or facial recognition. But many people still rely on passwords, and don’t even use the two-factor authentication now considered critical.
“As long as passwords are still part of the equation, they’re vulnerable,” Joy Chik, Microsoft’s vice president of identity, wrote in a September 2021 company blog post.
Here are six ways to stay protected.
Change identical user names, passwords fast, and first, on key accounts
For ease, many people use the same username and password across accounts, but it also puts them at significant risk of having their information compromised. Based on a sample of more than 39 million IoT and OT devices, about 20% used identical usernames and passwords, according to the Microsoft report.
If you fall into this category, it’s time to take action. Start by focusing on the biggest risks first — email, financial, health care and social media sites, said Chris Pierson, founder and chief executive of BlackCloak, a cybersecurity company that specializes in preventing targeted attacks on company employees and executives.
Telling a person who has many identical website logins and passwords to change them all at once is akin to advising someone to lose 50 pounds by running 20 miles a day and going cold turkey on sweets, he said. A more manageable starting recommendation would be a once-a-day 15-minute walk around the block and small dietary changes. The same is true when it comes to password protection, Pierson said. “Don’t change every single password you have. Focus on the highest risk, highest damage accounts.”
Use a password manager to encrypt your data
To keep track of passwords safely and efficiently, security professionals recommend using a secure password manager such as 1Password or KeePass. The user only has to remember one long strong password and the manager stores the others in an encrypted format. Password managers can also be used to generate secure, random passwords, which are exceedingly difficult to crack. Even though it requires relying on a third party, password managers generally do a good job of protecting customer data, said Justin Cappos, an associate professor at NYU Tandon School of Engineering whose focus includes cybersecurity and data privacy.
Choose strong passwords if you won’t use random generation
While randomly generated passwords are a best practice, not everyone likes using them, so at least make sure you’re using credentials that can’t easily be hacked. You might, for instance, string together four random words like sun, water, computer and chair for one account, and use another set of four words for a different account, said Roy Zur, founder and chief executive at cybersecurity training company ThriveDX Enterprise.
Using the phrase “moneycashcheckbank” for instance would take a computer about 23 million years to crack, according to a website maintained by Security.org, which reviews safety products. By contrast, the password “jesus” could be cracked instantly, while the same word with a capital “J” could be cracked in about 9 milliseconds, according to the website.
Enable multi-factor authentication
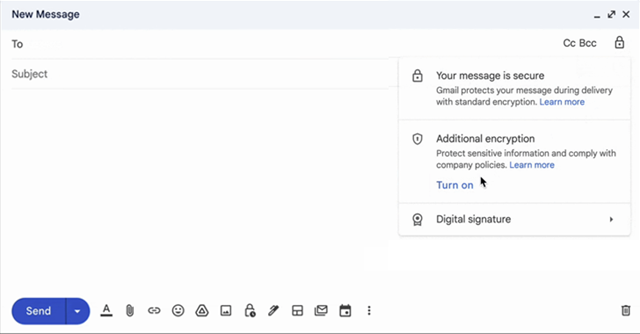
Some services such as Apple Pay mandate this extra layer of security for accounts. Even if a provider doesn’t require it to be used, multi-factor authentication is a valuable security tool that’s underutilized, according to security professionals.
The idea behind multi-factor authentication — which requires two or more pieces of identifying information — is to make it harder for criminals to infiltrate your accounts. Hackers target the weakest link “and your role is not to be the weakest link,” Zur said.
For these purposes, it’s advisable to use an app such as Google Authenticator or a hardware token like a YubiKey, instead of SMS, whenever possible, Cappos said. That’s because SMS is vulnerable to SIM swapping and other hacks. “It’s not difficult for a motivated hacker to get around SMS,” he said.
Google Voice e-commerce scam shows why you should never share a password
This is a problem that happens all too often, according to the Identity Theft Resource Center’s 2022 Business Impact Report. When asked about the root cause of an account takeover, 45% of companies said someone clicked on a phishing link or shared account credentials with someone who claimed to be a friend; 29% said someone shared account credentials with a hacker claiming to be a potential customer, vendor or prospect.
“Passwords are like gum. People shouldn’t share,” Cappos said.
Likewise, never give out a one-time code — even when scammers make the reason for sharing seem legitimate, said Eva Velasquez, president and chief executive of the Identity Theft Resource Center.
One increasingly common scam is where fraudsters pose as interested buyers on online marketplaces. They direct a seller to read off a one-time code allegedly sent by the buyer, often for the stated purpose of “verifying the seller’s identity and legitimacy” which reels victims in, Velasquez said. In reality, it’s a way for hackers to create a Google Voice account tied to the seller’s phone number. This allows scammers to perpetrate other scams using a Google Voice number that can’t be traced back to them, she said. The fraud has become so prominent that ITRC created an instructional video on how affected consumers can reclaim their number.
Apple or Microsoft contact you? It probably wasn’t them
In addition to having passwords or other sensitive information compromised by clicking on seemingly legitimate links in their email, texts or social media, people also tend to fall hard for tech support scams based on computer pop-ups or phone calls. Hackers may pretend to be from reputable companies such as Apple or Microsoft and offer to help with a security issue they’ve allegedly identified. Consumers get duped into allowing unfettered access to their computer, setting in motion the potential for thieves to steal their passwords and other personal data or insist on payment for bogus services rendered, Pierson said.
Remember, reputable companies don’t randomly contact consumers and offer to help with computer-related issues. Pierson said consumers shouldn’t engage with someone unfamiliar who reaches out, especially if that person’s information isn’t verifiable through independent and reliable means. “Googling a phone number is simply not something that we would advise either,” he said.
Source: CNBC