Expert who stopped spread of attack by activating software’s ‘kill switch’ says criminals will ‘change the code and start again’
The “accidental hero” who halted the global spread of an unprecedented ransomware attack by registering a garbled domain name hidden in the malware has warned the attack could be rebooted.
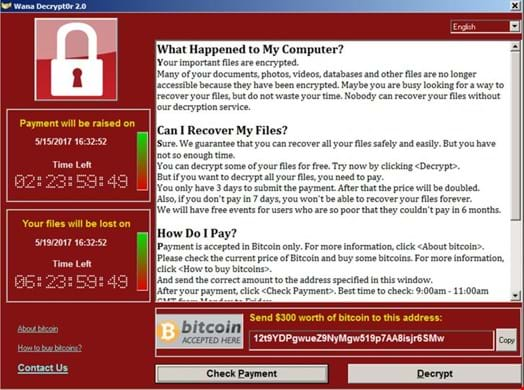
The ransomware used in Friday’s attack wreaked havoc on organisations including FedEx and Telefónica, as well as the UK’s National Health Service(NHS), where operations were cancelled, X-rays, test results and patient records became unavailable and phones did not work.
But the spread of the attack was brought to a sudden halt when one UK cybersecurity researcher tweeting as @malwaretechblog, with the help of Darien Huss from security firm Proofpoint, found and inadvertently activated a “kill switch” in the malicious software.
Disruption from cyber-attack to last for days, says NHS Digital – as it happened
British prime minister thanks NHS staff for working overnight after attack of ‘unprecedented’ scale
The researcher, who identified himself only as MalwareTech, is a 22-year-old from south-west England who works for Kryptos logic, an LA-based threat intelligence company.
“I was out having lunch with a friend and got back about 3pm and saw an influx of news articles about the NHS and various UK organisations being hit,” he told the Guardian. “I had a bit of a look into that and then I found a sample of the malware behind it, and saw that it was connecting out to a specific domain, which was not registered. So I picked it up not knowing what it did at the time.”
The kill switch was hardcoded into the malware in case the creator wanted to stop it spreading. This involved a very long nonsensical domain name that the malware makes a request to – just as if it was looking up any website – and if the request comes back and shows that the domain is live, the kill switch takes effect and the malware stops spreading. The domain cost $10.69 and was immediately registering thousands of connections every second.
MalwareTech explained that he bought the domain because his company tracks botnets, and by registering these domains they can get an insight into how the botnet is spreading. “The intent was to just monitor the spread and see if we could do anything about it later on. But we actually stopped the spread just by registering the domain,” he said. But the following hours were an “emotional rollercoaster”.
“Initially someone had reported the wrong way round that we had caused the infection by registering the domain, so I had a mini freakout until I realised it was actually the other way around and we had stopped it,” he said.
MalwareTech said he preferred to stay anonymous “because it just doesn’t make sense to give out my personal information, obviously we’re working against bad guys and they’re not going to be happy about this.”
He also said he planned to hold onto the URL, and he and colleagues were collecting the IPs and sending them off to law enforcement agencies so they can notify the infected victims, not all of whom are aware that they have been affected.
He warned people to patch their systems, adding: “This is not over. The attackers will realise how we stopped it, they’ll change the code and then they’ll start again. Enable windows update, update and then reboot.”
He said he got his first job out of school without any real qualifications, having skipped university to start up a tech blog and write software.
“It’s always been a hobby to me, I’m self-taught. I ended up getting a job out of my first botnet tracker, which the company I now work for saw and contacted me about, asking if I wanted a job. I’ve been working there a year and two months now.”
But the dark knight of the dark web still lives at home with his parents, which he joked was “so stereotypical”. His mum, he said, was aware of what had happened and was excited, but his dad hadn’t been home yet. “I’m sure my mother will inform him,” he said.
“It’s not going to be a lifestyle change, it’s just a five-minutes of fame sort of thing. It is quite crazy, I’ve not been able to check into my Twitter feed all day because it’s just been going too fast to read. Every time I refresh it it’s another 99 notifications.”
Proofpoint’s Ryan Kalember said the British researcher gets “the accidental hero award of the day”. “They didn’t realise how much it probably slowed down the spread of this ransomware”.
The time that @malwaretechblog registered the domain was too late to help Europe and Asia, where many organisations were affected. But it gave people in the US more time to develop immunity to the attack by patching their systems before they were infected, said Kalember.
Source: www.theguardian.com